In this blog post I am going to discuss how you can interact with basic blocks in IDAPython. Before we jump into the technical details, I want to provide some context and show why I became interested in exploring this feature of IDA Pro.
Background and Motivation
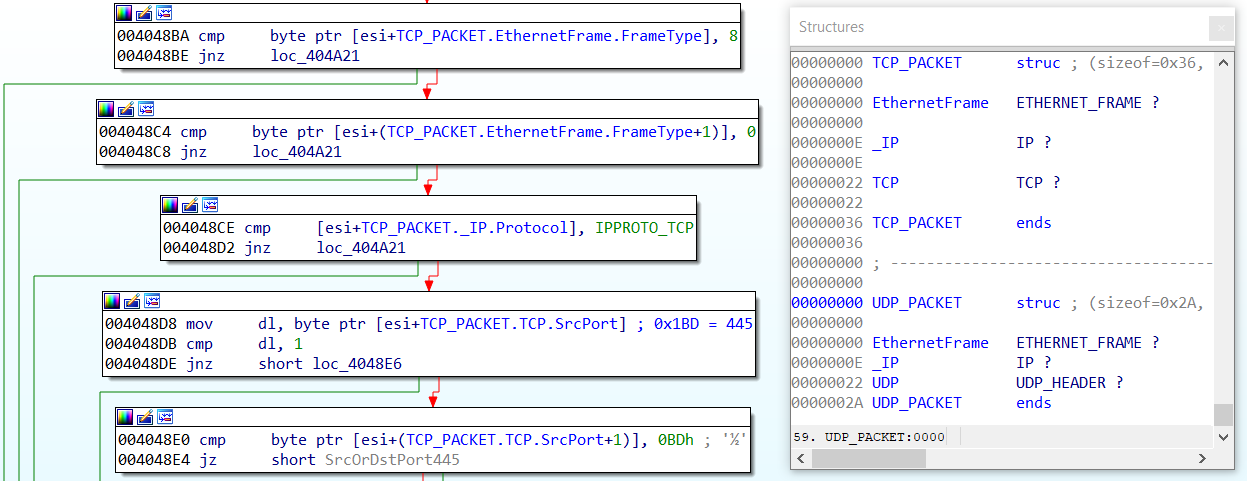
The other day I reverse engineered a backdoor that was heavily armored with two classic anti-disassembly techniques. The first technique substitutes jmp instructions with sequences of push and retn instructions. Figure 1 shows how this hinders the program’s control flow analysis. First, IDA Pro interprets the retn instruction to mark a function’s end. Second, IDA Pro is not able to identify the target addresses as code and hence does not disassemble them.
.text:00564A90 sub_564A90 proc near ; CODE XREF: ___tmainCRTStartup+10Dp
.text:00564A90 push 564C87h
.text:00564A95 retn
.text:00564A95 sub_564A90 endp
Figure 1
Figure 2 shows the same disassembly after I changed the push operand type to offset.
.text:00564A90 sub_564A90 proc near ; CODE XREF: ___tmainCRTStartup+10Dp
.text:00564A90 push (offset loc_564C83+4)
.text:00564A95 retn
.text:00564A95 sub_564A90 endp
Figure 2
Continue reading “IDA Pro Anti-Disassembly, Basic Blocks, and IDAPython”